See it in action
The following shows you some use-cases and how potential errors are caught by the script.
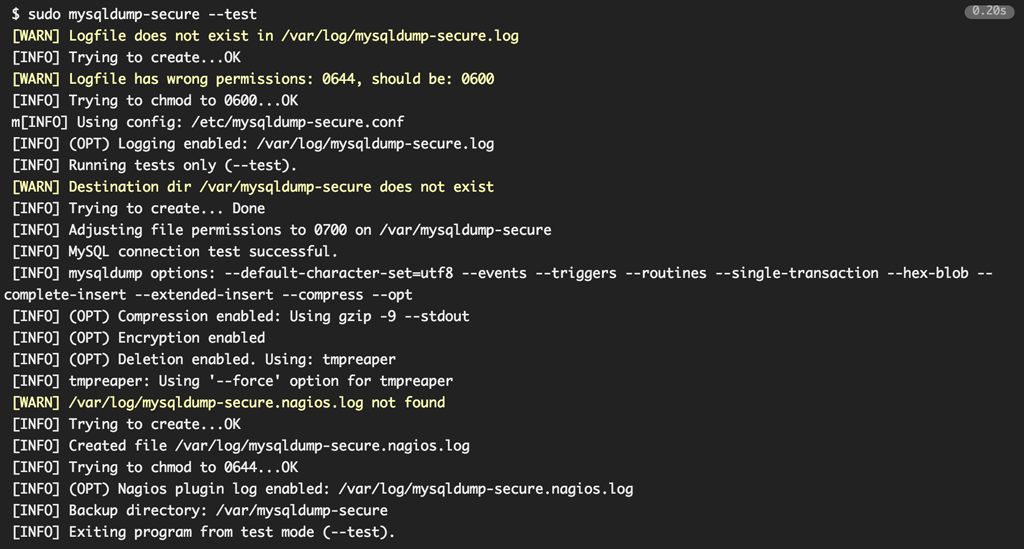
Test mode
During test mode (--test) you can see if mysqldump-secure is setup correctly and ready to run.
Note: All modes (test, cron and normal mode) will auto-fix any file or directory permissions.
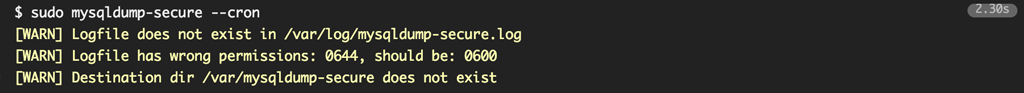
Cron mode
Without warnings or errors
When in cron mode (--cron) all info output will be surpressed (no output to stdout), so that your cronjob does not send any mails on sucessful run.

With warnings
If however the cron mode encounters problems (errors or warnings) it will output thos to stderr, so that cron error mails will be generated.
Note: If run from your crontab, the colorized output will be disabled, as there is no tty available to display colors anyway .
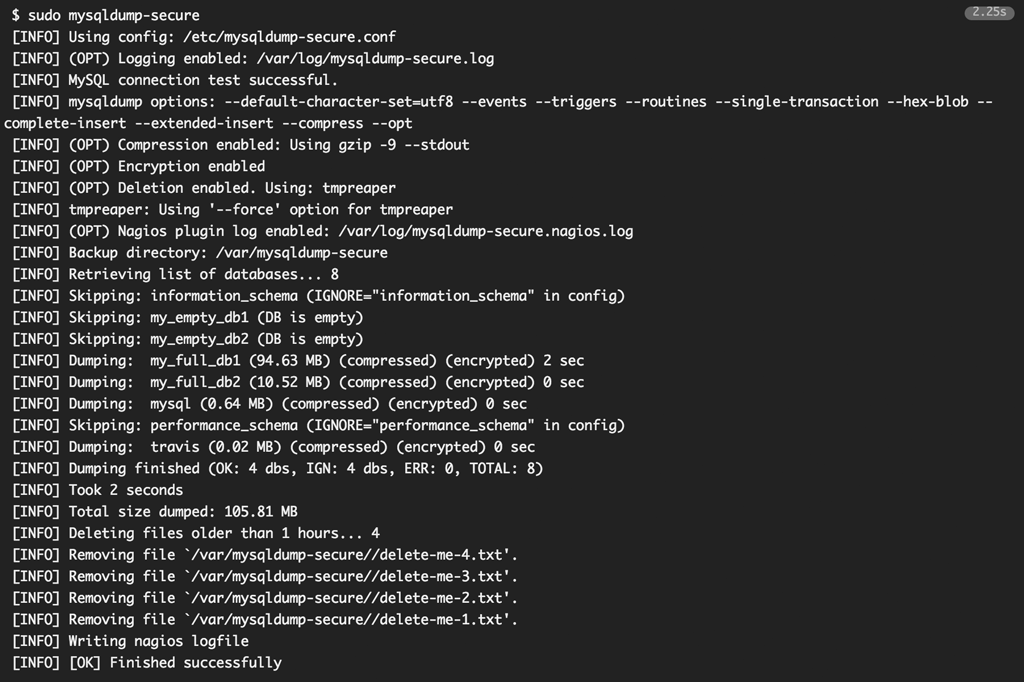
Normal mode
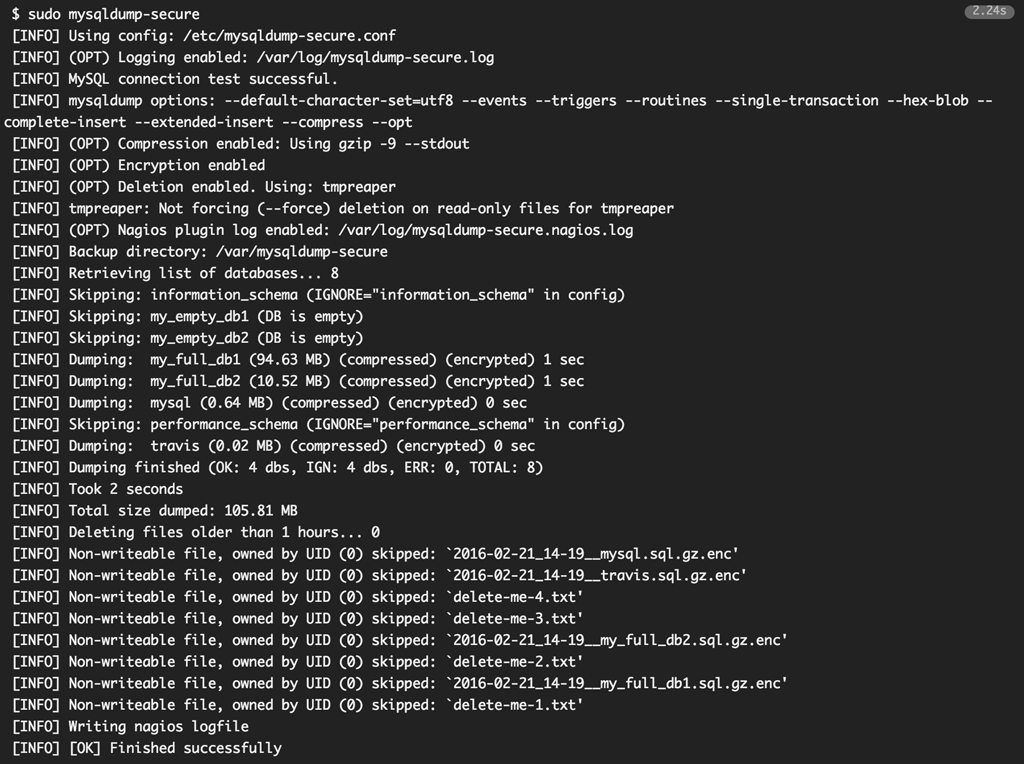
Fully featured dump
The following is an example with all available options enabled: encryption, compression, tmpreaper deletions logging and nagios log.
Tmpreaper complaining
The following shows an example when tmpreaper or tmpwatch is not able to delete read-only files (Because $FORCE_DELETE has been turned off).
Normal mode with errors
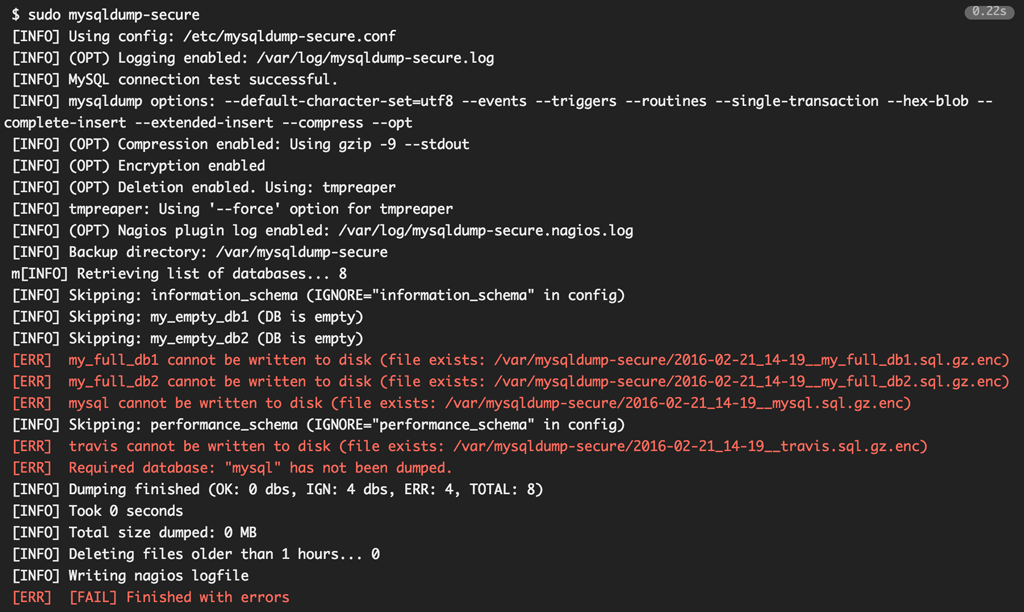
File with the same name exist
In case a dump file with the same name already exists, it will not be overwritten (could be an important dump). mysqldump-secure will still continue running and informs you about any encountered errors.
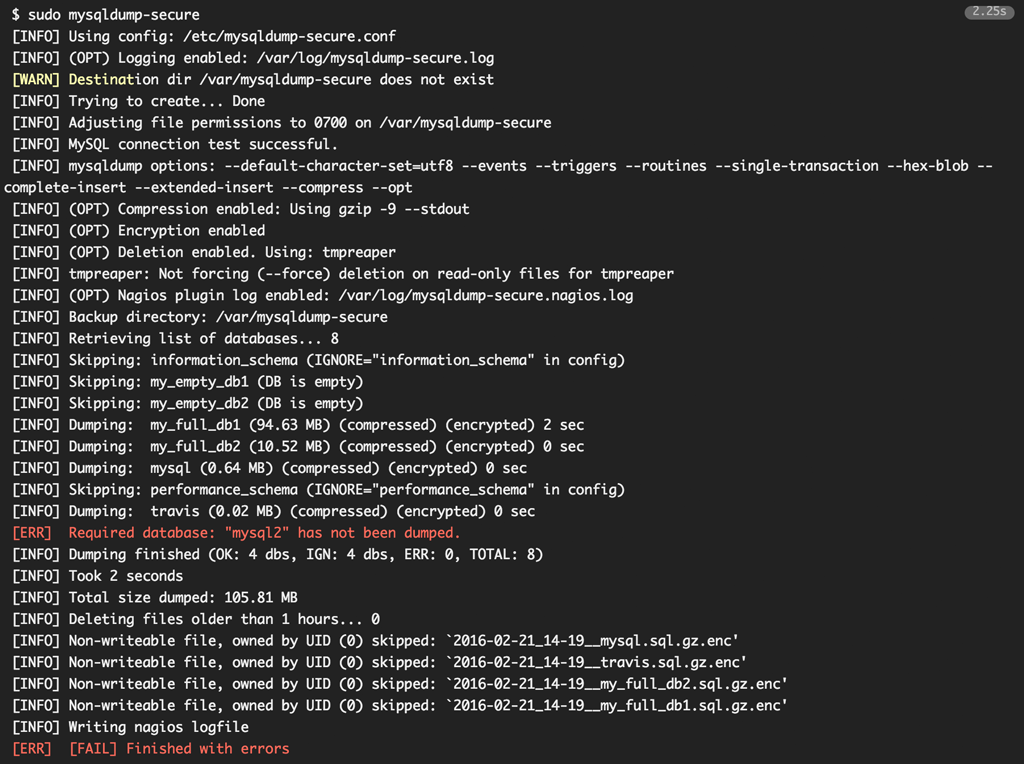
Missing required database
Let's say you have setup the script that a database called mysql2 must be dumped no matter what and this database does not seem to exist, the script will inform you with an error message during run-time and will exit >0 after it has finished normally .
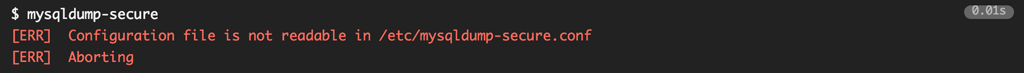
Configuration file not readable
mysqldump-secure will also check against its own configuration: Does the file exist, is it readable, do all variables exist in the configuration, do all variables have a meaningful and correct value, etc...
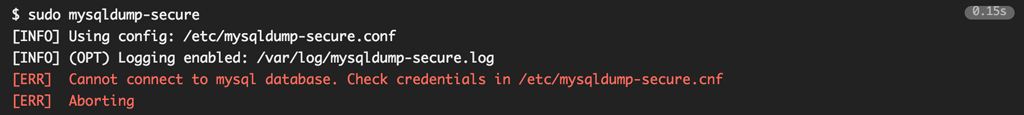
Wrong mysql credentials
mysqldump-secure will also check if the credentials file is properly protected and if the specified credentials work.